- Examples of Phishing attempts
- Examples of various types of “Phishing” attempts.
[Examples Gallery Update: 9/4/2014]
With the recent compromise of a number of celebrities iCloud Photo Streams there is, yet again, more focus on passwords, security and how to protect yourself.
In the case of this most recent attack the perpetrators simply attempted to use a number of common passwords along with figuring out the security questions to compromise the accounts in question. Apple has denied that iCloud was hacked by exploiting a hole in the “Find My iPhone” feature and that any exposed issue has been patched.
OK… but now what?
We need to better educate ourselves, our faculty, our students on how to protect themselves and their information as we ask them to do more and more online.
A few tips:
- To start, make sure you have a secure password. It should have a combination of upper and lowercase letters, include numbers and symbols and be greater than 8 characters long. Birth dates, anniversaries, family or pet names should be avoided as they can be easily guessed.
- This may sound simple, but don’t share you password with anyone. In school this is something that we tell our students and faculty upfront. At our school we have ways to solve you technical problems without you having to give us your password and if you school or organization doesn’t have a way to do that be sure to change your password frequently.
- Try using a password with a twist. If you don’t want to have a different password for every site and service you use try adding a prefix of suffix to your password for that particular service. You might use “MyS3cret_facebook” for Facebook and “MyS3cret_gmail” for your Google account.
- Enable two-step or two-factor verification for your accounts. While this will only really protect you against people changing you account information or password it is an added level of security to take when trying to secure your information online.
Phishing
“Give a man a fish and you feed him for a day; teach a man to “phish” and you feed him all your passwords…”
Phishing, as defined by Wikipedia is “… is the attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money) by masquerading as a trustworthy entity.”
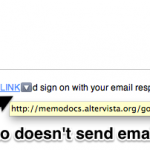
Phishing is frustrating because it can seem so real and the emails that come into you inbox can seem so legitimate. Last school year an email went out to the majority of the faculty at our school asking people to reset their passwords online and was signed “Technology Department”. Many of our conscientious faculty did as they were asked… problem was the email didn’t come from my department. Before we were aware of the email a number of people made the change and in a short period of time our email server was compromised and thousands of SPAM emails were being sent through our servers.
In the case of this email, the sending email address wasn’t from a school account, the message wasn’t signed by anyone from the school and their was no previous communication about the change prior to getting their email. We have made it clear to our faculty that prior to our department making any such request of them like this there would be much greater communication about such a change.
But what about the emails we get that look like they are coming from a valid sender and even have the correct logos and link included?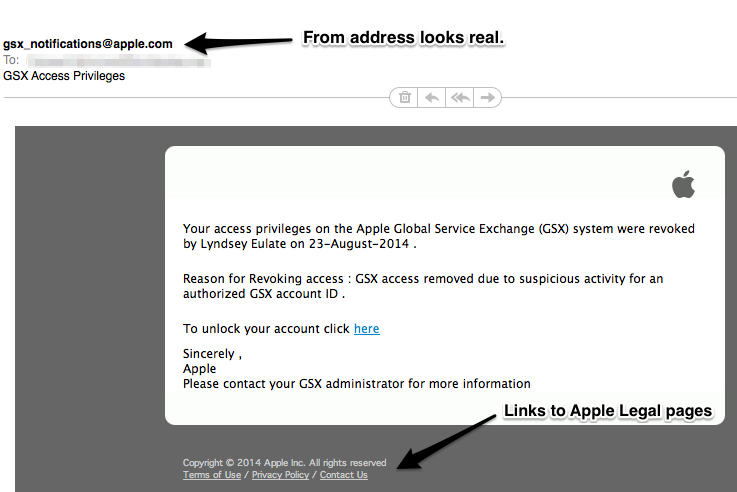
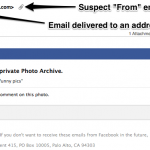
In the case of this email things look good. The sending address looks like it is from Apple and the links at the bottom of the email are to actual Apple pages. But what is “GSX”? This email went to an account for the parent’s association at our school and GSX is for the Apple Global Service Exchange. While we use GSX at school, the parent’s association doesn’t.
Lesson: If you don’t know what it is or why you are getting it, question it.
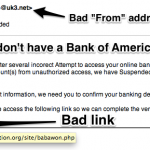
But what about that link in the email? The one that it telling you tot click “here”. Well, thankfully in this case when you click the email Safari actually picked up that there might be someone “phishy” going on and gives you a warning.
Lesson: If your browser is warning you about a page, think twice.
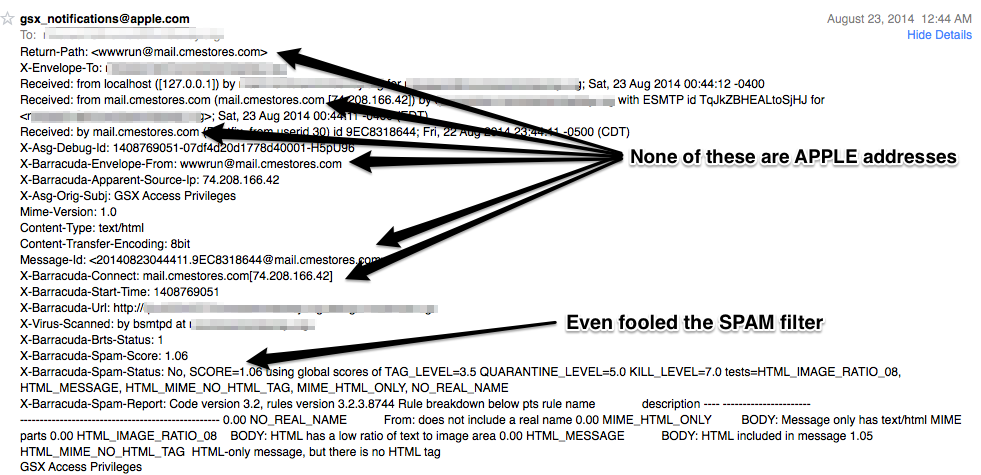
But what if you don’t get a warning like this? What if your just not sure? Show the “headers”.
![]() The header contains a lot of information about the message that you don’t normally seeing. It’s the routing information about where it came from, how it got there and where to send it back to if it can’t be delivered. In most email clients you can show the header information by selecting the option under a “View” menu.
The header contains a lot of information about the message that you don’t normally seeing. It’s the routing information about where it came from, how it got there and where to send it back to if it can’t be delivered. In most email clients you can show the header information by selecting the option under a “View” menu.
Looking at all of this can seem a little overwhelming, but if you know what to look for it’s easy. In this case you want to see email addresses or servers that have the apple.com somewhere in their address(es). In the case of this particular message it is clear that none of these come from Apple, rather cmestore.com which much like the example of our compromised email server may not even be the original sender of the message.
Lesson: Check out the “headers” when you’re really not sure.
When it all comes down to it there has always been shyster, scammers and people of low character that have been trying to con you out of your money or information. In the digital age it hasn’t gotten any easier, but there are ways to protect yourself and lessons that you can learn to help.
As we think about how we are preparing our students for the world as we require more technology use of them we need to be sure that we are not only teaching them to be productive learners, but also how to conduct and protect themselves in their digital worlds as well.
[2010 post of same topic: iTunes Phishing Receipt PSA]